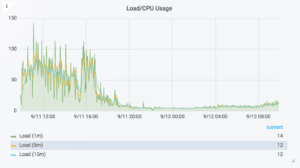
According to a new threat report by eSentire, IIS, Drupal, and Oracle WebLogic experienced an increased rate of IIS attacks in the second quarter of the year 2018. IIS, in particular, showed a drastic increase in the attacks from 2,000 to an astounding 1.7 million attacks during this time period.
eSentire Threat Intelligence analyzed the attacks and revealed that both IIS and WebLogic experienced a consistent number of 200 attacks per IP Address across organizations from servers hosting Apache, RDP, SQL, IIS, and HTTP API services.
The reports also revealed that most of the attacks originated from China-based IP Addresses with 3.5 million IIS servers exposed with one-third of that amount in the nation alone, largely originating from Alibaba and Tencent.
The attacking infrastructure also involved interesting conclusions to the operating systems. Over 400 attacking addresses were Windows machines hosting operating systems ranging from Windows XP to Windows 8.
Additionally, 350 FTP servers and over 100 mail servers were reported along with the presence of VPN servers, MikroTik devices (reported as bandwidth-testing servers), Kangle, Squid, Jetty, and a handful of lesser-known web service technologies.
The Q2 threat report also included other statistics revealing that the most affected sectors were biotechnology, accounting, real estate, marketing, and construction.
It also reported that the most common execution tactic technique observed around endpoint solutions was the use of PowerShell (32%), followed by VBA scripting (21%). Of the PowerShell-based attacks observed, 83% used obfuscated command lines intended to hide their intentions.
Emotet was also reported as the most frequently observed malware. The reports had various other findings in it.
The eSentire Threat Intelligence team used data gathered from 2,000+ proprietary network and host-based detection sensors distributed globally across multiple industries.
Raw data were normalized and aggregated using automated machine-based processing methods. Processed data was reviewed by a visual data analyst applying quantitative analysis methods.
Quantitative intelligence analysis results were further processed by a qualitative intelligence analyst resulting in a written analytical product.